Are you the weakest link? asks Monica Seeley
The cost and the common starting point
Cybercrime is estimated to cost business €1 trillion per year. Why is it so prevalent when most organisations have cast iron technological defences against phishing, malware and denial of service? Where is the weakest link? It is us, the users. We are our organisations’ biggest liability in the defence against cybercrime.
This is true for every organisation from boutique VA bureaus to the largest global enterprises. We are often time poor and speed is of the essence. Email dominates most business people’s lives, yet it is the number one vector for a cyberattack. 75% of all cyberattacks emanate from email; an email which, in our haste to clear our bulging inboxes, has been opened by accident.
Opening the door to the cybercriminal
Here are five easy entry points for the cybercriminal during a typical day:
1. En route to work
You buy a coffee and they greet you by name. The watching cybercriminal now has your name and can Google images to find you. Guesswork and a review of your social media sites tells them all they need about you to start an email attack, such as dumping malware or making a ransom demand.
2. Clearing your inbox
You see an email from a key contact – maybe the CEO – with the subject-line ‘Important’ or ‘Read This’. Maybe you booked a hotel or flight for your executive and an email comes back saying they cannot process the original credit card you used. In haste you respond. Bingo – the cybercriminal has scored with a phishing attack! The other common form of cyberattack is an email telling you the cybercriminal has access to your account and is making a ransom demand.
3. Lunchtime
You meet friends outside the office. During lunch you check your emails and leave your mobile device open/screen side up. It probably displays a picture of a loved one/pet or the company logo. You have again left key information clearly visible for the cybercriminal who may also be listening in via the Wi-Fi network and hearing and observing your keystrokes. Yes, with clever software a cybercriminal can eavesdrop as you type and transcribe the sounds into letters!
On your way back to the office you purchase something; clothes, toiletries, an item for your executive. The shop says they will email you the receipt rather than print one out, as they are part of the ‘Beat Receipt Campaign’. This campaign is aimed at helping save our planet because till receipts are not only toxic but responsible for cutting down more trees than printing newspapers. However, this creates another loophole because the shop now has your email address. Moreover, if the shop’s computers are hacked the cybercriminal has that data too. Whilst being a keen environmentalist, to me this is just another way of exposing your personal data to prying eyes.
4. Back at the office
You continue ploughing through your inbox and sending emails with attachments in raw Office files (eg Word, Excel, PowerPoint). You answer a request from a participant at a talk your executive gave recently. Inadvertently, you send the files to James.Smith@ instead of James_Smith. Easily done. However, once again information which can be misused has been disclosed to prying eyes. It has happened to Google, Wholefoods and Barclays to name a few.
Then, you close up ready to take a break for a few days and set your Out of Office message something like the one below.
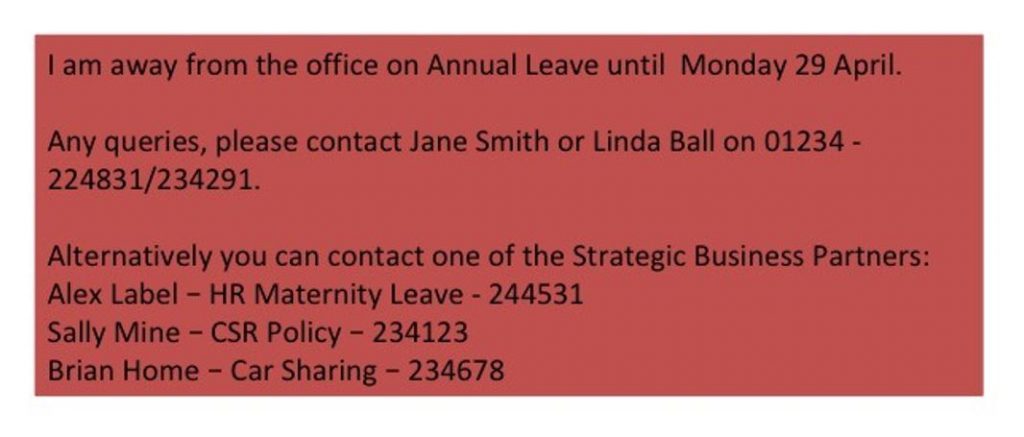
It would not take a cybercriminal five minutes to find out where you live. You return to a burglary.
5. At home on social media
You post your latest workout statistics, then login with one of your social media accounts to buy something online. Two more gaping holes created. Most sports activity sites have been hacked at some point to reveal the person’s preferred regime, route (and hence home address), personal effects such as a bike, and the time when the person is active. If the website you went to is hacked or, worse still, is a fake, the cybercriminal now has your social media account details and more.
It’s not surprising we time-poor humans are the biggest liability to our business’s plans to minimise cyberattacks.
So, here are ten key ways we can help reduce the risks of a cyberattack.
In public places
1. Always be on your guard: look around at who is nearby and how they are behaving.
2. Use a fake name when ordering food in very public places like coffee bars and fast food shops.
3. Keep all mobile devices either closed or face down when not in use.
4. Have respect for email. Take time when dealing with your inbox no matter how busy you are.
5. Phone senders if you are the slightest bit suspicious about an email. Often the sender will not know their account has been hacked until you call.
6. Turn off all auto-fill functions, especially those in Outlook.
7. Set a safe, simple Out of Office message which gives nothing away. With an Out of Office message, simplicity rules.

It’s rather like a dummy burglar alarm. The cybercriminal now has no idea if it’s just you on a business trip or the whole family is away. So, they will move on to a more revealing message. It is not unknown for cybercriminals to use the Out of Office (OOO) message to blag their way into the office and gain access to important files – or even the whole IT system!
If you are an Outlook user remember that you can create two OOO messages; you might want to include more information on the internal message. Nonetheless, some organisations ban external OOOs on the basis that if you are an important business partner or client you will have been given alternative contact information.
If you do use an OOO, make sure your switchboard and/or reception knows that you are away. They are often the first point of contact once the cybercriminal has your OOO and wants to find out more information (such as whether to blag their way into the office or burgle your home).
Social media
8. Minimise the use of your social media login details outside of the relevant sites. Facebook recently revealed it had exposed the data of millions of users.
Passwords
9. Change your passwords frequently; at least every three to six months. Ensure you create a strong password or use a password management app.
10. Always use multi-factor authentication when you can.
Now you have gone from being a major liability to the first line of defence in a cyberattack!